Homepage > AXS Guard O&P – Managed Cybersecurity Platform
AXS Guard Observe & Protect is a comprehensive, high-performance and user-friendly platform that allows companies and IT partners to manage every aspect of their cybersecurity while improving their cyber resilience.
Our solution provides comprehensive protection for all your digital assets through multi-layered security measures. It is based on a zero-trust approach to effectively prevent cyberattacks. No matter your budget or IT environment, we have the perfect solution for your organization.
We also offer customized plans to cater to your specific needs.

It’s not just in smaller companies they lack a security team. No matter how competent, the general IT guy is unlikely to be able to defend the company against ransomware syndicates. He or the IT team is completely overwhelmed by day-to-day operations, meaning cybersecurity is reactive, not proactive. They only look at security when something is already on fire.
And besides that, outside of office hours, they may have other things going on called life. Most companies are not organized in a way they can monitor everything around the clock.
In case there is a security team, it’s not easy to find qualified staff. True experts are few and far between, which is why they are in high demand and expensive. And they aren’t scalable, but human; which means it’s not unthinkable they suffer from ‘alert fatigue’.
Also hackers are using autonomous AI agents to do reconnaissance, find misconfigurations in cloud environments, and write exploit scripts in a matter of minutes. By extensively automating activities based on AI, victims are caught up in the speed.
Methods such as triple extortion ransomware and supply chain hopping are on the rise, but by tomorrow, hackers will have already devised new techniques. Hard to keep up.
Our Privileged Access Management solutions secure elevated access, enhance visibility, and prevent unauthorised access.
We implement robust controls to protect critical assets, reduce risks, and ensure compliance across cloud, hybrid, and on-premises environments.
Enterprise clients are now forcing their smaller vendors to prove their cyber hygiene before signing a contract. Suddenly, the smaller company is hit with a Vendor Risk Assessment in response to, for example, NIS2. If they can’t prove their security maturity, they might lose their biggest contracts. They are bleeding revenue because of bad security.
Say goodbye to cybersecurity worries and hello to total peace of mind. AXS Guard offers a comprehensive, fully adaptable solution to meet your unique business needs.
Observe & Protect is a Managed Cybersecurity Service based on a Belgian engineered and developed platform. Relying on these services means you have a dedicated Cybersecurity SOC (Security Operations Center) team at your disposal. Our trained SOC engineers and analysts monitor security alerts 24/7, ensuring immediate action whenever a threat arises.
This services formula introduces the opportunity to get affordable, enterprise-grade cybersecurity to organizations of all sizes.
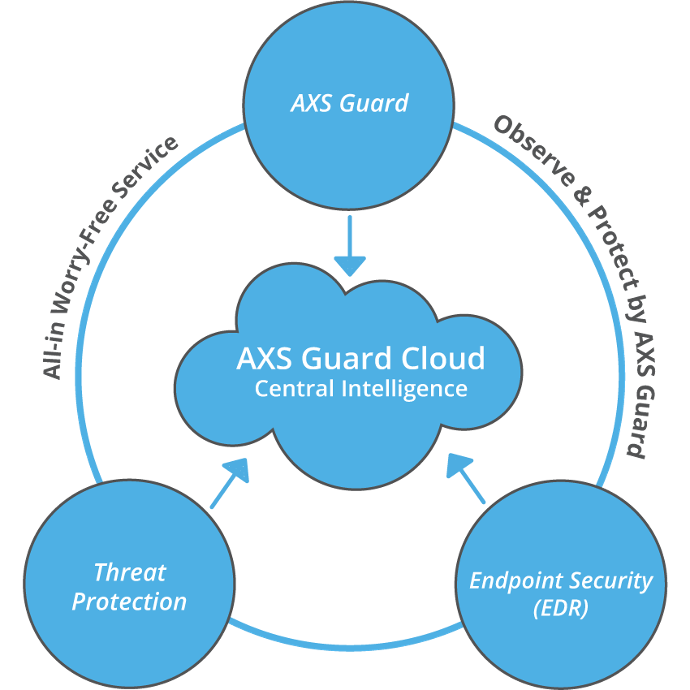
AXS Guard Observe & Protect is a multi-layered cybersecurity solution designed to safeguard your networks and empower your organization with robust cyber resilience. We take a holistic approach to prevent cyberattacks and keep your data secure.
Observe & Protect equips you with a comprehensive suite of tools to manage every aspect of your cybersecurity.
Our powerful solution delivers optimal security without compromising network efficiency.

Observe & Protect is built for accessibility, empowering IT professionals and everyday users to navigate the platform with ease.

We prioritize proactive defense, employing advanced techniques to detect and stop cyberattacks before they can infiltrate your systems.
Our solution adheres to the zero-trust model, assuming no user or device is inherently trustworthy. This ensures continuous verification and minimizes security risks.
This powerful platform provides all the features you need to securely connect your organization to the internet.

Protect the devices across your network, including computers, laptops, tablets, mobile devices, and IoT endpoints.

Proactively identifies and blocks threats through GeoIP filtering, DNS security and web and mail content scanning.
Effortlessly manage deployments, settings, system issues, and gain real-time threat insights.
Unmatched Peace of Mind
Securing your IT infrastructure is a critical responsibility. Managed Cybersecurity Services via a SOC provide the reassurance of constant vigilance by cybersecurity specialists, so you can focus on running your business.
Proactive Threat Detection
Continuous monitoring safeguards your networks, systems, and data. Identifying and addressing potential breaches early, minimizes risk and maximizes protection.
Compliance Simplified
Many industries face complex cybersecurity regulations such as NIS2, GDPR, HIPAA, and ISO 27001. Making use of a Managed Cybersecurity Platform ensures your compliance with these standards, saving valuable time and resources.
Digital Sovereignty
AXS Guard’s Observe & Protect – an integral part of Approach Cyber – is based on inhouse technology: engineered, developed and assembled in Belgium. Companies can stop outsourcing their survival to ‘foreign black boxes’ and take control with a platform built for sovereignty – in Europe, managed by local experts.
Cost-Effective Security
Building and maintaining an in-house cybersecurity team can be expensive. AXS Guard’s managed services eliminate the need for significant upfront investments and ongoing personnel costs.
Expert Threat Management
Benefit from our team’s deep knowledge and experience in cybersecurity. We can analyze, assess, and address even the most sophisticated threats, keeping your data and operations safe.
Scalable and Flexible
Whether you’re a small startup or a large enterprise, AXS Guard’s managed cybersecurity services can be tailored to your specific needs and business goals.

Your organisation must take responsibility for managing cyber risks, navigating complex regulatory landscapes, and meeting legal obligations.
Our tailored GRC solutions enhance your security and compliance posture, while supporting business continuity, through the adoption of effective standards and certifications.

Safeguarding personal data is critical due to evolving data protection regulations. Our solutions ensure your organisation remains compliant while protecting against data breaches.
Proactive privacy management is essential to avoid penalties, reputational damage, and to foster trust in your services.

The growing volume and complexity of data, coupled with AI’s rise, present challenges for organizations. Effective data security and governance are crucial for compliance, informed decision-making, and misuse protection.
Our solutions transform data into reliable assets for strategic insightful decisions.

In the evolving cyber landscape, you face heightened vulnerabilities due to sophisticated hacker tactics, including AI-enhanced threats.
Our Ethical Hacking solutions, such as penetration testing and advanced red and purple teaming exercises, are essential for identifying vulnerabilities and strengthening security posture.

Our Threat Detection & Response solutions address the increasing sophisticated cyber threats.
We provide 24/7 protection through our in-house SOC, utilizing Managed XDR for rapid threat detection, effective incident response and forensics, and proactive monitoring of vulnerabilities across your digital landscape.
As applications grow in importance, we shift security left by embedding it throughout the development lifecycle.
Our solutions include secure development assessments, methods, advanced tools, trainings, and advisory, along with outsourced software development, ensuring robust and secure applications.
Our team of experts is ready to help you start your journey towards cyber serenity.